We are the crew that keeps your ship running at full speed - proactively managing every layer of your environment so you can navigate with confidence, focus on your mission, and reach your destination without disruption.
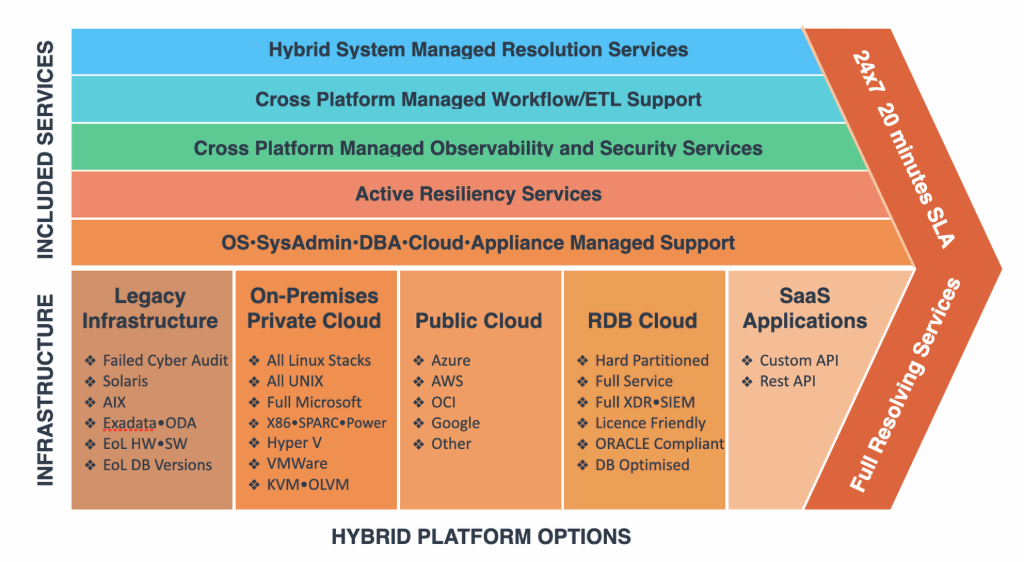
End-to-end performance, resilience, and control
Complete oversight from infrastructure to application layer, ensuring performance, resilience, and security across your entire environment
Secure, scalable desktop access from anywhere
Delivers secure, scalable virtual desktops, giving users reliable access to applications and data from anywhere
Reliable, optimised databases - secure and always on
Provides 24/7 monitoring, optimisation, and support across all major database platforms, ensuring availability, performance, and security for your critical data
Continuous control of hybrid and cloud systems
Delivers 24/7 monitoring and management of on-premises, hybrid, and cloud infrastructure, ensuring secure, reliable, and optimised performance across servers, storage, and networks
Secure, resilient, and optimised connectivity
Provides 24/7 monitoring and management of network and perimeter devices, ensuring secure, optimised, and resilient connectivity across your entire environment
Central visibility for rapid root-cause analysis
Delivers 24/7 alerting, Elastic-based centralised log management, and observability for network and perimeter devices, providing centralised visibility, intelligent correlation, and rapid root-cause analysis to strengthen security, streamline troubleshooting, and ensure continuous performance