We are your watchman at the helm, navigating the ever-changing threat landscape to keep your organisation secure, resilient, and ready for anything.
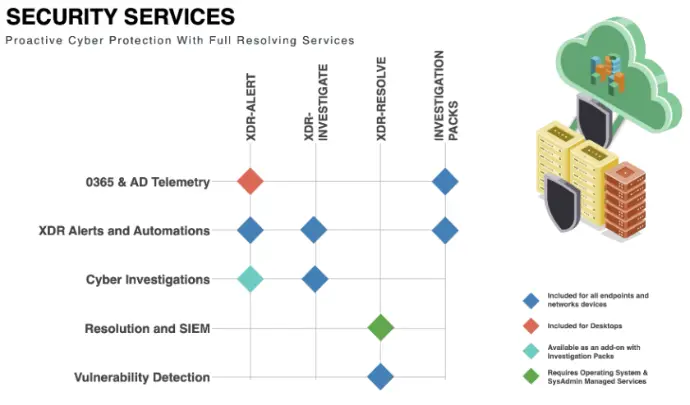
Complete protection from alert to resolution
Combining XDR Alert, Investigate, and Resolve into a comprehensive, end-to-end cybersecurity solution
End-to-end security assessment and assurance
A comprehensive, end-to-end evaluation of your infrastructure, operating systems, and database security posture
Continuous detection and remediation of risks
Our vulnerability management service combines continuous scanning, assessment, and remediation with real-world threat intelligence to keep your environment secure and resilient
Reduce risk exposure and build resilience
Minimise risk exposure while empowering customers to plan strategically and respond with greater speed and confidence
Identify weaknesses before attackers do
Our Security Health Check provides a comprehensive evaluation of your IT environment to identify vulnerabilities, misconfigurations, and compliance gaps
Prepare confidently for certification success
Our Cyber Essentials Readiness service helps organisations prepare for certification by assessing current controls, identifying gaps, and aligning policies and processes with Cyber Essentials requirements